Disabling SSLv2 support in IIS
If you have undergone a “Trustkeeper Scan” and failed due to your Microsoft web server using SSLv2, then read on.
NOTE: PLEASE READ THIS POST IN OUR BLOG HERE. It is TWO YEARS NEWER and simplifies most of the tasks regarding SSL settings.
SSLv2 is considered a “medium” security risk and will cause your scan to FAIL, so therefore to be PCI-DSS compliant (for credit card companies), you need to disable it via the registry on your Windows server running IIS 3 or later.
The easiest way to do this is to read this KB article from Microsoft.
In a nutshell, you need to go to this registry key
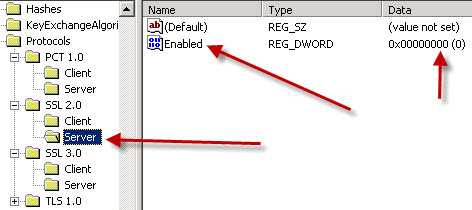
HKey_Local_Machine\System\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols
- Click on the “Server” node.
- On the Edit menu, click Add Value.
- In the Data Type list, click DWORD.
- In the Value Name box, type Enabled, and then click OK. Note: If this value is present, just double-click the value to edit its current value.
- Type 00000000 in Binary Editor to set the value of the new key equal to “0”.
- Click OK. Restart the computer
- if applicable, reschedule the security scan